JustIAM¶
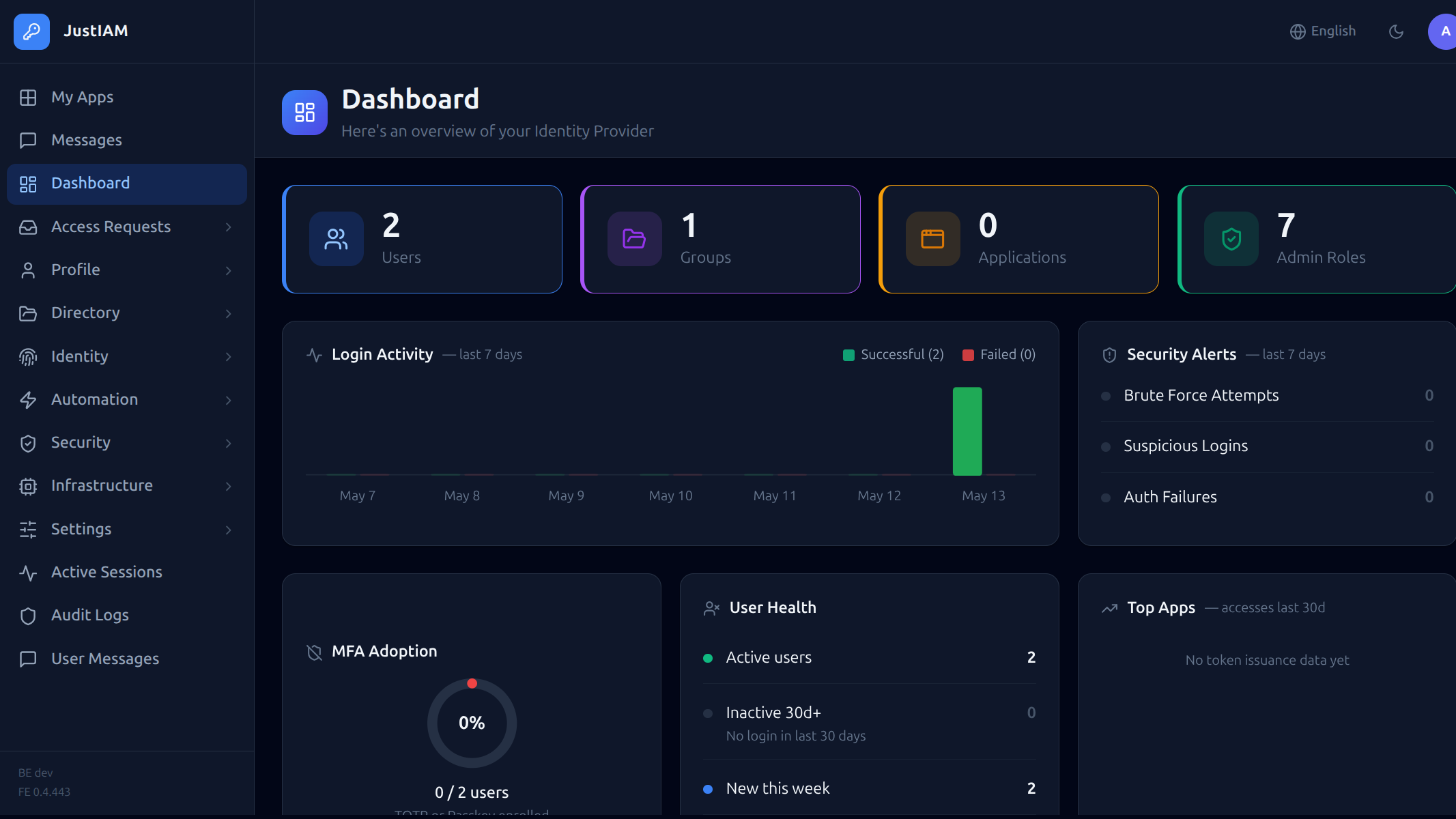
JustIAM is a self-hosted Identity Provider that gives you full control over authentication and authorization for your applications. It provides a modern web UI for day-to-day administration and exposes a comprehensive REST API and Terraform provider for infrastructure-as-code workflows.
What it does¶
| Feature | Description |
|---|---|
| OIDC / OAuth2 | Acts as a standards-compliant OpenID Connect Provider (Authorization Code + PKCE, refresh tokens) |
| SAML 2.0 | Full SP-initiated SSO, IdP-initiated SSO, Single Logout, attribute mapping |
| Local accounts | Email/password login with configurable password policy and lockout |
| Federated login | Google OAuth2 (and extensible to others) with domain/email whitelisting |
| MFA | TOTP (authenticator apps) and passkeys (FIDO2/WebAuthn) |
| RBAC | Fine-grained IDP roles control who can administer which resources |
| App role mappings | Per-user / per-group values injected into OIDC claims and SAML attributes |
| Audit log | Immutable event log with IP, user agent, and structured details |
| Multi-tenant | Single backend instance serves multiple isolated tenants, each at its own hostname |
| Terraform provider | Full IaC support for all resources |
Architecture¶
Browser / Application
│
▼
┌─────────────────┐
│ Frontend (SPA) │ React + TypeScript + Tailwind
└────────┬────────┘
│ REST API
┌────────▼────────┐
│ Backend (Go) │ Gin, pgx, RS256 JWTs
└────────┬────────┘
│ per-tenant
┌────────▼────────┐
│ PostgreSQL │ one DB per tenant
└─────────────────┘
In multi-tenant mode each tenant is resolved from the Host header (acme.totmicro.com → tenant acme). All per-tenant state (DB pool, JWT secret, OIDC key pair, task runner, event worker) is isolated in a TenantContext and never shared across tenants.
Tenant configuration is loaded from Kubernetes Secrets at startup (production) or a YAML file (development). See k8s-mt/ for the production manifests.
Quick links¶
- Installation → — Kubernetes setup (single-tenant
k8s/and multi-tenantk8s-mt/) - Docker Compose → — Local development and self-hosted deployment
- Configuration → — Environment variables and tenant config
- OIDC integration → — Connect your application
- SAML integration → — Enterprise SSO
- Terraform → — Manage JustIAM as code
- Script Examples → — Ready-to-use scripts for tasks, events, MFA, and claims
- Licensing → — License tiers, activation, and renewal
- Control Plane → — Multi-tenant management
- API reference → — Full REST API docs